News Articles
FileChecker WordPress Plugin
Those who attempt to seize control of WordPress sites often do so by burying obfuscated code in the PHP scripts of plugins, themes or the WordPress core. This is done through various exploits in improperly secured PHP, less-restricted file system permissions, or server counter-measures.
The following are examples of PHP functions that are commonly used to exploit WordPress, along with some extremely simplified examples of how they may be used.
base64_decode
base64_decode can used to un-obfuscate malicious code from what appears to be a benign string of letters and numbers.
PHP Manual »
<?php
$bad = "PHNjcmlwdD5hbGVydCgncHduZWQnKTs8L3NjcmlwdD4=";
$decoded = base64_decode($bad);
echo $decoded;
?>
str_rot13
str_rot13 can be used to un-obfuscate malicious code from what appears to be a benign string of letters and numbers.
PHP Manual »
<?php
$bad = "<fpevcg>nyreg('cjarq');</fpevcg>";
$decoded = str_rot13($bad);
echo $decoded;
?>gzinflate
gzinflate can be used to un-obfuscate malicious code (deflate data format) from what appears to be a benign hash of characters and symbols.
PHP Manual »
<?php
$bad = gzdeflate("<script>alert('pwned');</script>");
echo gzinflate($bad);
?>fwrite
fwrite can be used in conjunction with the above obfuscation functions to write to the file system a new (or temporary) script that contains malicious code.
PHP Manual »
<?php
bad("<script>alert('pwned');</script>");
function bad($code) {
$tmpf = stream_get_meta_data ( $tmp = tmpfile() ); fwrite( $tmp, $code );
$ret = include ( $tmpf ['uri'] ); fclose ( $tmp ); return $ret;
}
?>
eval
eval can be used in conjunction with the above obfuscation functions to execute decoded or re-assembled code.
PHP Manual »
<?php
eval('$bad="<script' .
'>alert(\'pwne' .
'd\');</script' .
'>";');
echo $bad;
?>To assist in identifying where your WordPress scripts may have been corrupted, we offer a plugin to run a background search (grep) on the directory of your server’s file system where you have WordPress installed.
The matches found are only presented to you, the user of the plugin, and are not shared.
Future versions of this plugin may introduce community-based analysis of the matched results, to help you to determine if these lines of code are harmless and for the effective function of the website’s core, theme or plugins, or if they have been injected into your scripts for malicious intent.
FileChecker Does…
To un-obfuscate and run the malicious code, a common list of PHP functions is often used, such as: base64_decode(), str_rot13(), gzinflate(), fwrite(), and eval(). This plugin runs a command-line search through the entire WordPress file system to find these functions so that you can analyze them as genuine or problematic. Once verified, you can choose to ignore a harmless script so that it is no longer presented for your review.
FileChecker Does Not…
The plugin does not repair or clean your scripts, but merely checks the file system for instances of these functions for your own individual analysis. It is our hope that it will provide insight and help identify attacks quickly, and before any permanent damage is done. Furthermore, it is recommended that you ask your host to maintain nightly backups of your site and database so that they may be restored in the event an attack occurs.
Ask the Community
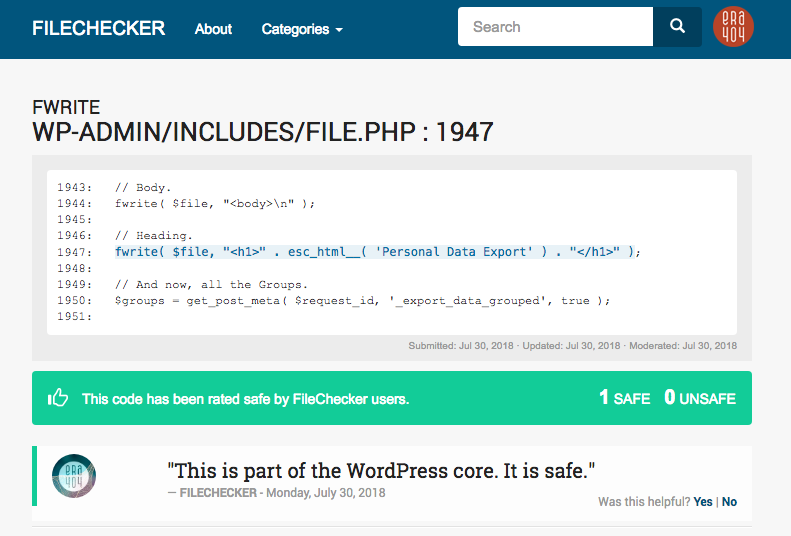 It’s the collaborative nature of WordPress that has not only accelerated its growth, but also introduced some of the exploits that this plugin is designed to identify. FileChecker embraces this collective powerhouse, by giving users the ability to have their own site files checked against the code evaluations submitted by others. Advanced WordPress users who identify code as harmless can publish these results publicly to FileChecker.net so that others can probe the community to determine the integrity of their own site’s scripts.
It’s the collaborative nature of WordPress that has not only accelerated its growth, but also introduced some of the exploits that this plugin is designed to identify. FileChecker embraces this collective powerhouse, by giving users the ability to have their own site files checked against the code evaluations submitted by others. Advanced WordPress users who identify code as harmless can publish these results publicly to FileChecker.net so that others can probe the community to determine the integrity of their own site’s scripts.
FileChecker WordPress Plugin
Other Plugins by ERA404
Permalink: https://www.era404.com/news/filechecker/